How *Not* To Implement A Web Application That Handles External Authentication, Using BeTwittered.com As An Example
 Today I'm going to look at how not to handle user authentication in a web application, taking BeTwittered.com authenticating with Twitter as an example (sorry, guys).
Today I'm going to look at how not to handle user authentication in a web application, taking BeTwittered.com authenticating with Twitter as an example (sorry, guys).
BeTwittered is a simple and comfortable gadget that you can add to your site, such as your iGoogle homepage.
Since BeTwittered is just a bridge between you and Twitter, it has to first log you into your account. Here is where things go horribly, horribly wrong.
1. BeTwittered does not use SSL to secure requests to its servers
All authentication information is transmitted to BeTwittered servers in plain text and is easily sniffable by an attacker, both on your own network and outside of it. You can read more about SSL encryption here….
 Ever since the introduction of the official Retweet button, I've wanted it to be a little more interactive. I usually want to add my 2 cents into the tweet I'm about to retweet but the default RT button just doesn't allow for it – Yes is the only option:
Ever since the introduction of the official Retweet button, I've wanted it to be a little more interactive. I usually want to add my 2 cents into the tweet I'm about to retweet but the default RT button just doesn't allow for it – Yes is the only option:
![]()
Troy's Twitter Script
Enter Troy's Twitter script for Firefox that I reviewed in detail a few months ago.
Troy's script added the RT button to my stream (along with inline picture and video embed, auto url expander and shortener, name autocomplete, and other things) way before Twitter introduced it.
It also allowed me to add a couple of words or rephrase the retweet to make it more relevant to my followers….
Updated: August 5th, 2011
 And the winner is… the same guy who made headlines today because he tweeted from the altar at his own wedding – Dana Hanna.
And the winner is… the same guy who made headlines today because he tweeted from the altar at his own wedding – Dana Hanna.
Are his other tweets just as original as "Standing at the altar with @TracyPage where just a second ago, she became my wife! Gotta go, time to kiss my bride. #weddingday"?
Not so much… After looking at TheSoftwareJedi's (that's our Dana) timeline out of curiosity, I saw the following gem which definitely takes The Most Useless Tweet To Date award in my book. Here it is:
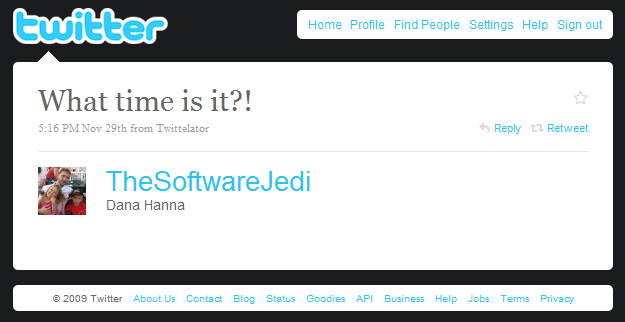
Yup, it's real and it was not rhetorical or followed up by some witty response. Nope. This was it.
Well, the answer is right there, Dana, …
The Real Reasons To Use Twitter (Get Over Your Prejudice Already)
Updated: May 22nd, 2009
Introduction
Let’s face it – the majority of the population doesn’t understand twitter. They don’t get its true value – all they see is an obnoxious social network full of exhibitionists tweeting about millions of mundane things of every minute of their lives.
Except, twitter is much, much more than that. In addition to all the wankers talking about themselves 24/7, of course. Twitter is what you make it to be. You can follow boring, uninteresting people with interests in growing cactuses (cacti?) and collecting fur balls. But you can also follow people sharing piles of interesting and useful information (see bullet points below). Just do me one favor and repeat after me: twitter is not only for publishing your …
Updated: September 16th, 2012
Recently I read an article on the Six Revisions blog that discussed 10 seemingly simple improvements to the twitter interface. They included such things as nick autocomplete, mentions, groups, and more.
You could only dream about such twitter improvements… that is until you use the Troys Twitter script. Just perform the following steps and you will have the features I describe in this article. Here we go:
- Install Firefox (you already have that, right?)
- Install the Firefox greasemonkey extension
- Install the Troys Twitter script
…
Random Questions and Thoughts. Password Protected Garage Door Remotes, Twitter Security, MUNI Drivers, Burgers, etc
Updated: July 1st, 2010
 From time to time my, still curious, mind accumulates a variety of questions and concerns which it has to spill onto the pages of this blog. How random are these? Pretty damn random, and I need to see some answers, quick. Oh, and I’m deliberately not searching Google, as I want to facilitate discussion. What fun would it be if I just looked up all these?
From time to time my, still curious, mind accumulates a variety of questions and concerns which it has to spill onto the pages of this blog. How random are these? Pretty damn random, and I need to see some answers, quick. Oh, and I’m deliberately not searching Google, as I want to facilitate discussion. What fun would it be if I just looked up all these?
Password Protected Garage Door Remotes
As a paranoid person and a recent homeowner, I started to wonder how safe I actually am in my house. Consider this likely scenario that nobody seems to be concerned with:
I park my car outside for one night and don’t take out my portable garage door remote, the
…
Read the rest of this article »
Updated: June 24th, 2020
 Introduction
Introduction
Clickjacking is a malicious technique of tricking web users into revealing confidential information or taking control of their computer while clicking on seemingly innocuous web pages. A vulnerability across a variety of browsers and platforms, a clickjacking takes the form of embedded code or script that can execute without the user's knowledge, such as clicking on a button that appears to perform another function (credit: Wikipedia).
Clickjacking is hard to combat. From a technical standpoint, the attack is executed using a combination of CSS and iFrames, which are both harmless web technologies, and relies mostly on tricking users by means of social engineering. Additionally, the only server side technique against clickjacking known to me is “frame breaking…
Artem’s Top 10 Tech Predictions And Ideas For 2009 And Beyond
 Everyone and their mother are throwing out their predictions for 2009 nowadays, it’s a new fad. It’s like you’re not cool anymore if you don’t have twitter, a Mac, and a set of random predictions for the next 12 joyous months.
Everyone and their mother are throwing out their predictions for 2009 nowadays, it’s a new fad. It’s like you’re not cool anymore if you don’t have twitter, a Mac, and a set of random predictions for the next 12 joyous months.
So I decided to throw in a few ideas of my own to be part of the cool crowd again (how much cooler can I be already, you might think, and I wouldn’t blame you).
Disclaimer (read it, tough guy)
What this post is:
Top 10 Reasons Why Digsby ROCKS
Updated: August 20th, 2009
If you haven't heard of Digsby yet, you have probably been living in some kind of a virtual cave or have no friends. Digsby is a multi-network instant messenger application, similar to Trillian, Pidgin (GAIM), or Miranda. I said 'similar', so what makes Digsy special? Reviews I read so far don't give the real reasons and don't dive into the features in depth. Instead, you get a standard load of marketing BS and in the end to you, the user, Digsby may end up being "yet another IM program." Some reviews describe certain features, but so far I haven't seen one that highlighted THE MAIN REASON why Digsby is different. And may I preface it with: finally somebody got a …
